You’d be hard-pressed to find a business owner with no understanding of phishing emails, ransomware, and other highly publicized threats to their business technology and data. However, it’s risky to assume that all your bases are already covered. Cyber threats evolve at a rapid rate as antiviruses struggle to keep up. Is your business as protected as it truly should be?
The next cybersecurity threat could easily come through one of these common IT vulnerabilities. Here’s where you should tighten security ASAP. #Enstep #cybersecurity Share on X
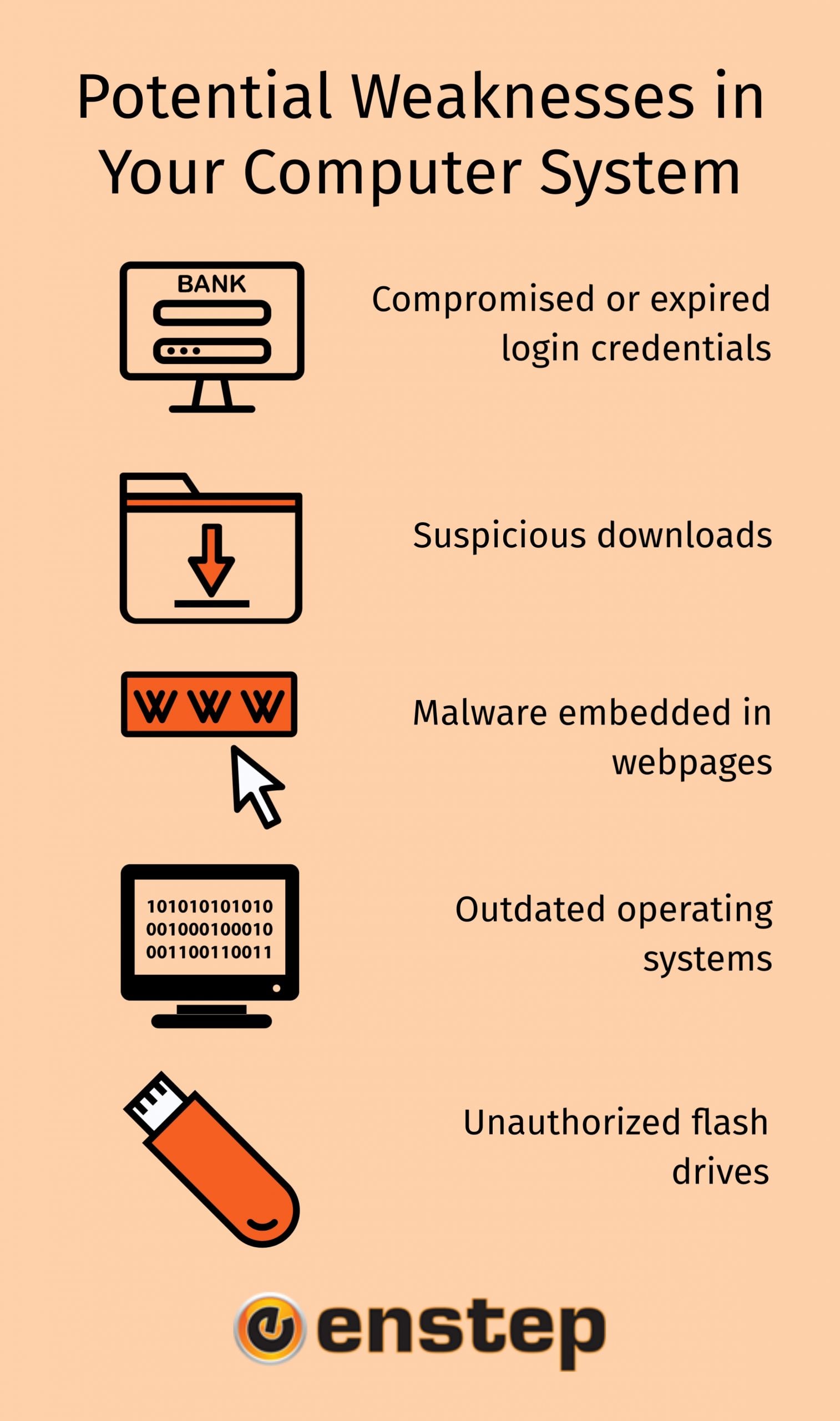
Potential Weaknesses in Your System
If you’ve already taken the time to examine and enhance your computer security, good work! But don’t stop there. Even seemingly innocuous things could become potential security holes that leave your system vulnerable. Here are a few additional factors to consider in your security strategy:
- Compromised or expired login credentials
- Suspicious downloads
- Malware embedded in webpages
- Outdated operating systems
- Unauthorized flash drives
1) Compromised or Expired Login Credentials
Everyone knows the importance of keeping usernames and passwords secure. But in practice, some people may feel comfortable sharing this information with coworkers or friends in a moment of need. This is risky enough. But even if the coworker is entirely trustworthy and doesn’t abuse their newfound account access, if their computer’s security is compromised, a hacker could easily gain access to your login credentials through them. It’s simply not worth the risk.
Another possible vulnerability comes from former employees or anyone who no longer requires account access. Leaving their login credentials active allows them to log back in when they have no business doing so, leaving your company vulnerable. And once again, even a trustworthy individual could find their computer was hacked and all their login information was stolen. Don’t leave unused accounts active.
2) Suspicious Downloads
Downloading files from the internet is an important part of many workdays. However, not every download is trustworthy. Some malicious downloads will even begin automatically in the background without the user’s knowledge. For these and other reasons, it may be a good choice for employers to install filtering software that blocks downloads from certain websites, or even allows downloads only from a few approved sites. Keep track of what’s being downloaded, when, and what it does.
3) Malware Embedded in Webpages
A particularly insidious type of malware embeds itself in webpages and infects your computer when you simply visit the page in question. Avoiding sketchy websites will usually keep this problem to a minimum, but even seemingly secure websites can hide threats in the background. Since there isn’t always a way to determine if a page is completely safe, opting for real-time security monitoring will be a lifesaver here. Let the experts see if you’re placing yourself in danger.
Pro Tip: Some emails come with embedded malware too, making even opening the email without clicking any attachments dangerous. Delete spam emails right away without opening them.
4) Outdated Operating Systems
Software updates aren’t (usually) just designed to make the developers more money. Operating system updates generally boast improved functionality, a cleaner layout, and most importantly, enhanced security. Continuing to use outdated software when a more secure version is available leaves you vulnerable to viruses that have long since cracked the code on the older version. Simply updating to the new and improved system can decrease your security vulnerability by a significant amount.
5) Unauthorized Flash Drives
While it may seem surprising to some, flash drives are still a staple of computer usage today. They offer a secure way to store information offline for a long time and share it easily. Unfortunately, they also allow for quick virus infections. While it’s unwise to completely ban flash drives from your workspace, make sure your computer’s security programs scan the drive for any errors or malware before granting access to its contents.
Reducing IT Vulnerabilities & Risks
Cybercriminals are smart, and will never stop trying to access and steal your sensitive data. Don’t let them get the edge on you! Assess your business for any and all potential IT vulnerabilities and make sure there’s no way for hackers to get in.
Connect with us for more information on keeping your business technology system strong.