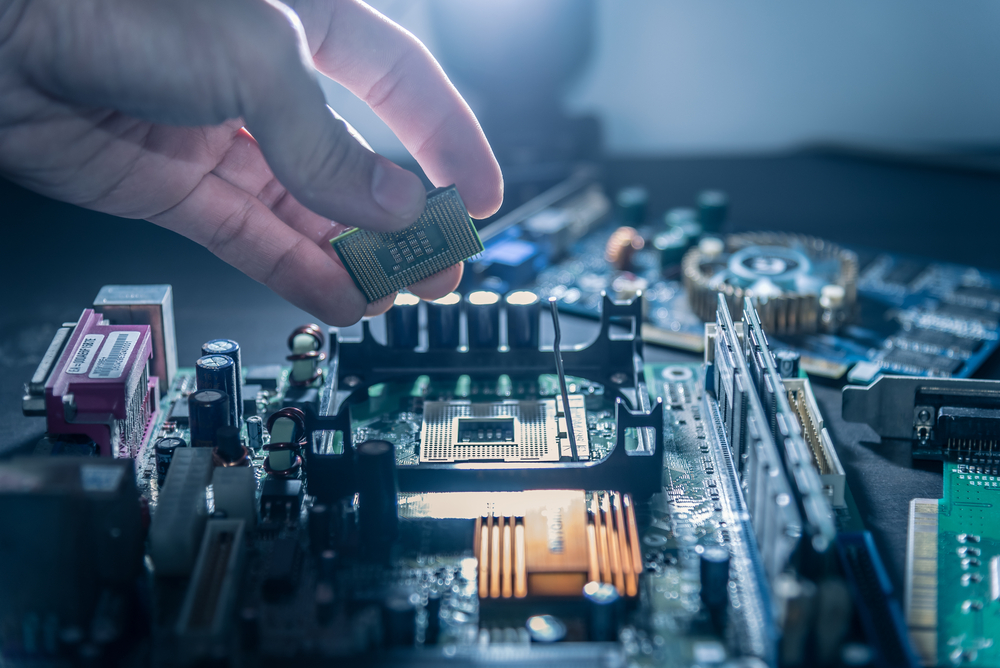
Certain models of counterfeit IT hardware are so convincing that even experts struggle to identify them as fake. Off-brand hardware isn’t inherently bad, but outright counterfeit parts pose a significant threat to your IT setup. Worse, if they’re subtle enough, you may not discover the problem until these fakes have been integrated for a long time.
Some counterfeit IT hardware is harmless aside from being of far inferior quality and offering a lower performance than the genuine equipment. However, several companies that have discovered counterfeit hardware in their systems also discovered significant security issues originating from the fakes. Don’t leave your business vulnerable! Let’s take a closer look at counterfeit hardware and how to identify it.
How do you tell if your IT setup has fake hardware? Here are the signs counterfeit hardware products have infiltrated your system. #Enstep Share on X
The Danger of Counterfeit Hardware Products
The biggest danger of fake hardware products is that they can potentially compromise your system’s security. According to IEEE Spectrum, counterfeit hardware products could contain malware that can destabilize your IT setup. This malware could go undetected for a while since counterfeit hardware is designed to bypass your system’s authentication process.
If your business is infiltrated with many counterfeit hardware products, you run the risk of significant financial and operational issues. You’ll lose a lot of business data when your IT setup breaks down, and that will translate into financial losses. It always pays to ensure your hardware is completely legitimate and safe.
Signs of Potential Fake Hardware
So, what are the signs your IT setup has fake hardware products? The biggest sign is whether or not the product in question continues working after an update. Counterfeit products are designed to bypass processes authenticating system components, but they don’t update along with your system. Any update will cause these fake parts to stop working. If anything stops responding immediately following an update, you very likely have counterfeit hardware in your setup.
Pro Tip: Whenever you add new hardware to your IT setup, verify it and then update your software as a second form of authentication. Fake hardware won’t work after an update.
Securing Your Business IT Setup
The best way to secure your business IT setup against fake hardware is by performing regular authenticity checks and software updates. You also need to purchase hardware products only from reputable and authorized resellers. Finally, check for physical differences that exist between different hardware units of the same product. Every little bit helps to keep your system secure.
Contact us to learn more about differentiating between fake hardware and genuine products.